Download CompTIA SecurityX Certification.CAS-005.ExamTopics.2025-09-25.131q.vcex
| Vendor: | CompTIA |
| Exam Code: | CAS-005 |
| Exam Name: | CompTIA SecurityX Certification |
| Date: | Sep 25, 2025 |
| File Size: | 3 MB |
| Downloads: | 18 |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Discount: 20%
Demo Questions
Question 1
IoCs were missed during a recent security incident due to the reliance on a signature-based detection platform. A security engineer must recommend a solution that can be implemented to address this shortcoming. Which of the following would be the most appropriate recommendation?
- FIM
- SASE
- UEBA
- CSPM
- EAP
Correct answer: D
Explanation:
D: 8 - Mosted D: 8 - Mosted
Question 2
A security engineer is reviewing event logs because an employee successfully connected a personal Windows laptop to the corporate network, which is against company policy. Company policy allows all Windows 10 and 11 laptops to connect to the system as long as the MDM agent installed by IT is running. Only compliant devices can connect, and the logic in the system to evaluate compliant laptops is as follows:
Which of the following most likely occurred when the employee connected a personally owned Windows laptop and was allowed on the network?
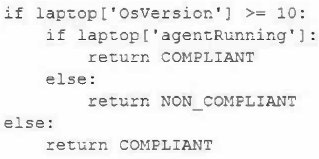
- The agent was not running on the laptop, which triggered a false positive.
- The OS was a valid version, but the MDM agent was not installed, triggering a true positive.
- The OS was running a Windows version below 10 and triggered a false negative.
- The OS version was higher than 11, and the MDM agent was running, triggering a true negative.
Correct answer: C
Explanation:
B: 1 - MostedC: 1 B: 1 - MostedC: 1
Question 3
During an adversarial simulation exercise, an external team was able to gain access to sensitive information and systems without the organization detecting this activity. Which of the following mitigation strategies should the organization use to best resolve the findings?
- Configuring a honeypot for adversary characterization
- Leveraging simulators for attackers
- Setting up a honey network for attackers
- Utilizing decoy accounts and documents
Correct answer: D
Explanation:
A: 1D: 4 A: 1D: 4
Question 4
A security architect discovers the following while reviewing code for a company's website: selection = "SELECT Item FROM Catalog WHERE ItemID = " & Request("ItemID")
Which of the following should the security architect recommend?
- Client-side processing
- Query parameterization
- Data normalization
- Escape character blocking
- URL encoding
Correct answer: B
Explanation:
B: 4 - Mosted B: 4 - Mosted
Question 5
A security architect needs to enable a container orchestrator for DevSecOps and SOAR initiatives. The engineer has discovered that several Ansible YAML files used for the automation of configuration management have the following content:
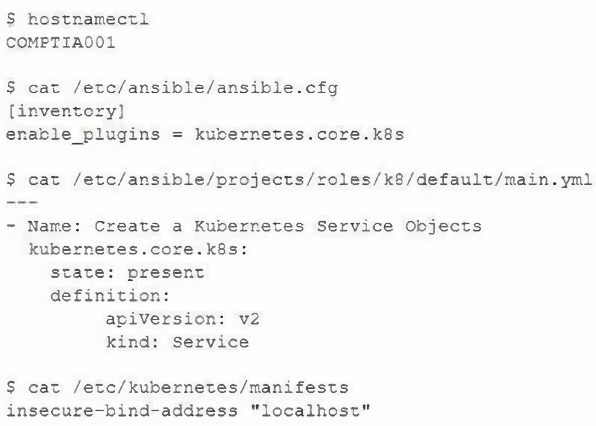
Which of the following should the engineer do to correct the security issues presented within this content?
- Update the kubernetes.core.k8s module to kubernetes.core.k8s_service in the main.yml file.
- Update the COMPTIA001 hostname to localhost using the hostnamectl command.
- Update the state: present module to state: absent in the main.yml file.
- Update or remove the ansible.cfg file.
- Update the insecure-bind-address from localhost to the COMPTIA001 in the manifests file.
Correct answer: D
Explanation:
E: 2 E: 2
Question 6
A CRM company leverages a CSP PaaS service to host and publish Its SaaS product. Recently, a large customer requested that all infrastructure components must meet strict regulatory requirements, including configuration management, patch management, and life-cycle management. Which of the following organizations is responsible for ensuring those regulatory requirements are met?
- The CRM company
- The CRM company's customer
- The CSP
- The regulatory body
Correct answer: A
Explanation:
A: 2 A: 2
Question 7
Company A is merging with Company B. Company A is a small, local company. Company B has a large, global presence. The two companies have a lot of duplication in their IT systems, processes, and procedures. On the new Chief Information Officer's (CIO's) first day, a fire breaks out at Company B's main data center. Which of the following actions should the CIO take first?
- Determine whether the incident response plan has been tested at both companies, and use it to respond.
- Review the incident response plans, and engage the disaster recovery plan while relying on the IT leaders from both companies.
- Ensure hot, warm, and mobile disaster recovery sites are available, and give an update to the companies' leadership teams.
- Initiate Company A's IT systems processes and procedures, assess the damage, and perform a BIA.
Correct answer: B
Explanation:
B: 2 B: 2
Question 8
The results of an internal audit indicate several employees reused passwords that were previously included in a published list of compromised passwords.
The company has the following employee password policy:
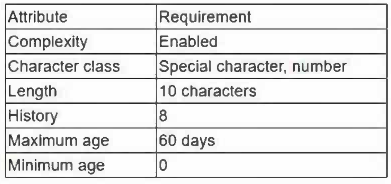
Which of the following should be implemented to best address the password reuse issue? (Choose two.)
- Increase the minimum age to two days.
- Increase the history to 20.
- Increase the character length to 12.
- Add case-sensitive requirements to character class.
- Decrease the maximum age to 30 days.
- Remove the complexity requirements.
- Increase the maximum age to 120 days.
Correct answer: AB
Explanation:
AB: 3BC: 1 - Mosted AB: 3BC: 1 - Mosted
Question 9
A security analyst is investigating a possible insider threat incident that involves the use of an unauthorized USB from a shared account to exfiltrate data. The event did not create an alert. The analyst has confirmed the USB hardware ID is not on the device allow list, but has not yet confirmed the owner of the USB device. Which of the following actions should the analyst take next?
- Classify the incident as a false positive.
- Classify the incident as a false negative.
- Classify the incident as a true positive.
- Classify the incident as a true negative.
Correct answer: B
Explanation:
B: 2 B: 2
Question 10
Which of the following security features do email signatures provide?
- Non-repudiation
- Body encryption
- Code signing
- Sender authentication
- Chain of custody
Correct answer: A
Explanation:
A: 3 A: 3
Question 11
A software development company wants to ensure that users can confirm the software is legitimate when installing it. Which of the following is the best way for the company to achieve this security objective?
- Code signing
- Non-repudiation
- Key escrow
- Private keys
Correct answer: A
Explanation:
A: 2 A: 2
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX AND EXAM FILES
Use ProfExam Simulator to open VCEX and EXAM files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!




